CyberMaterial HackHavoc CTF
Overview
This CTF was hosted by CyberMaterial and featured a variety of challenges across multiple domains including Web, OSINT, Forensics, and Cryptography.
Challenges Solved
Welcome To CyberMaterial
Challenge Description
OLD CTF
Solution
Flag can be found in “#ctf-support” channel description in the discord server.
Flag
CM{Subscribe_TO_CyberMaterial}
FeedBack Challenge
Challenge Description
OLD CTF
Solution
Flag can be found in final feedback Google Form.
Flag
CM{HApPy_EnDiNg}
Rev is easy!
Challenge Description
OLD CTF
Solution
Provided a file with no extension. Adding “.txt” , we can see its contents. Flag can be found in it.
Flag
CM{ReV_i5_Easy}
Who’s Really Dunked?
Challenge Description
OLD CTF
Solution
Provided Cipher text, convert it with Base92. Then again with ROT47. We get a JS code and tracing it flag is found.
Flag
CM{News_Alerts_Incident}
The Key to Nowhere
Challenge Description
OLD CTF
Solution
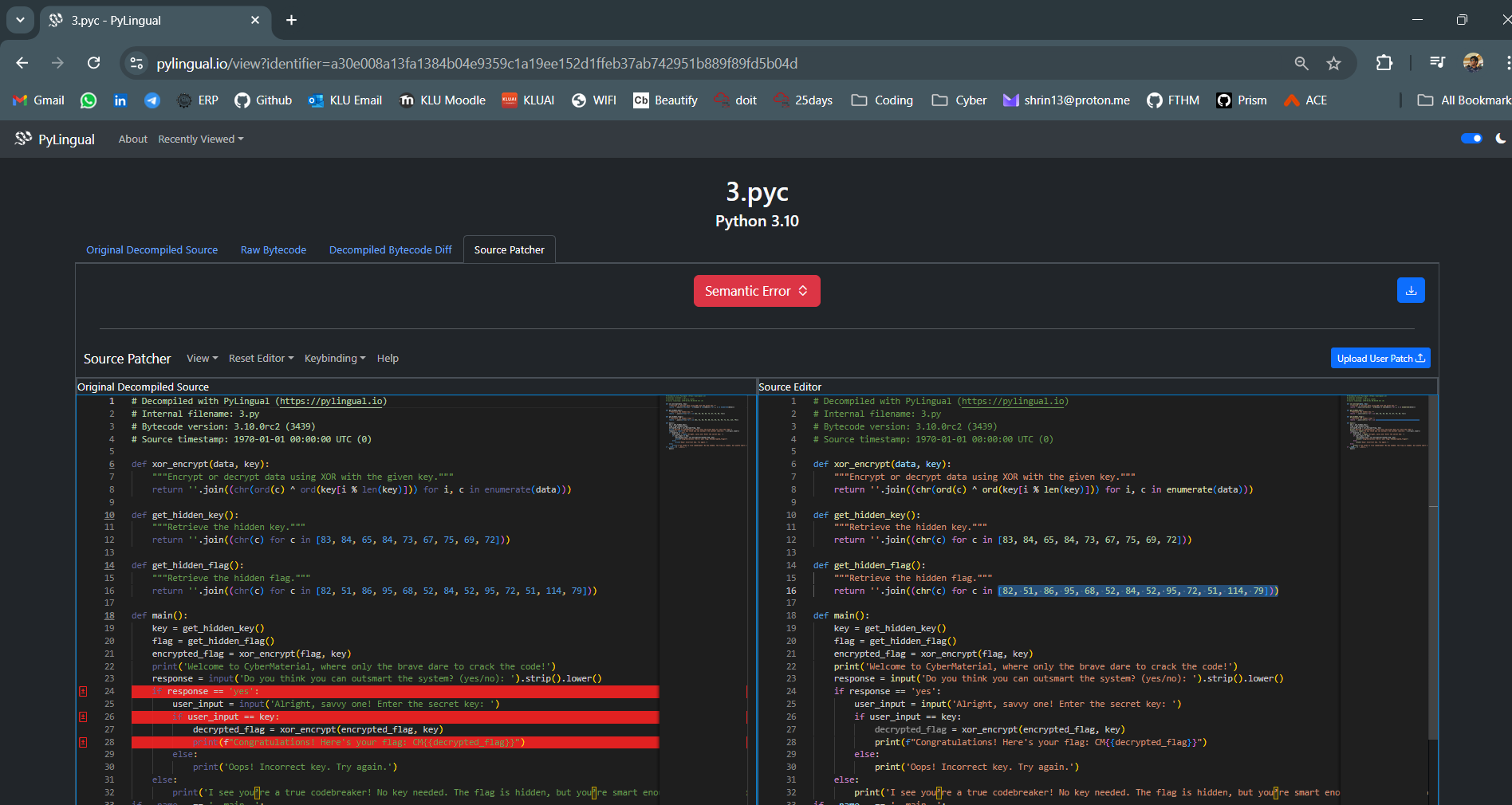
Given with a file with no extension, when we convert it to “.txt” we can see its content. Inside it we can see “PyInstaller” letting us know it is a file complied by PyInstaller.
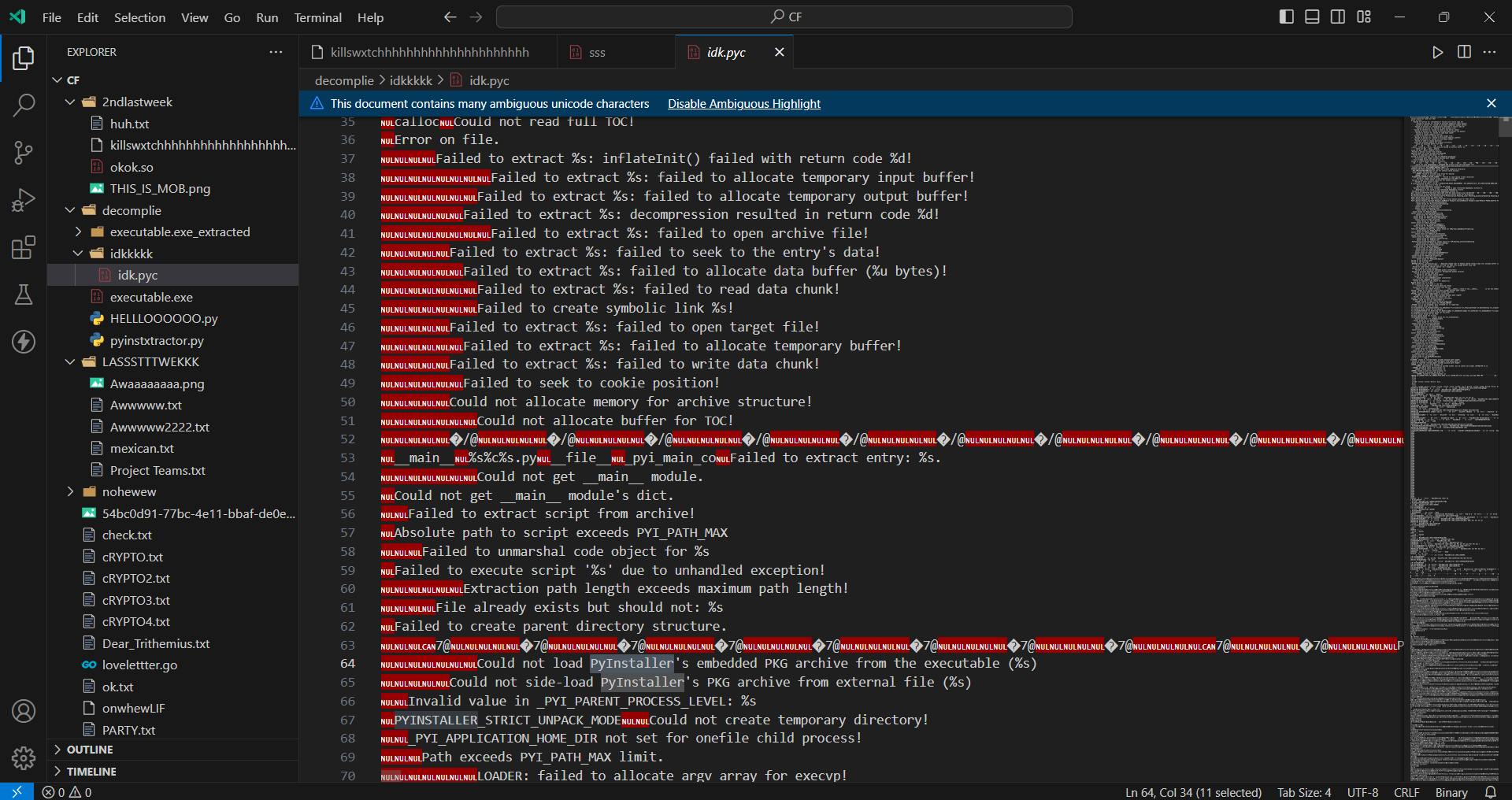
We can decompile the file with https://github.com/extremecoders-re/pyinstxtractor .
We get a “.pyc” file, we can convert that file to get the original Python code.
Flag
CM{R3V_D4T4_H3rO}
Go Crazy!!
Challenge Description
OLD CTF
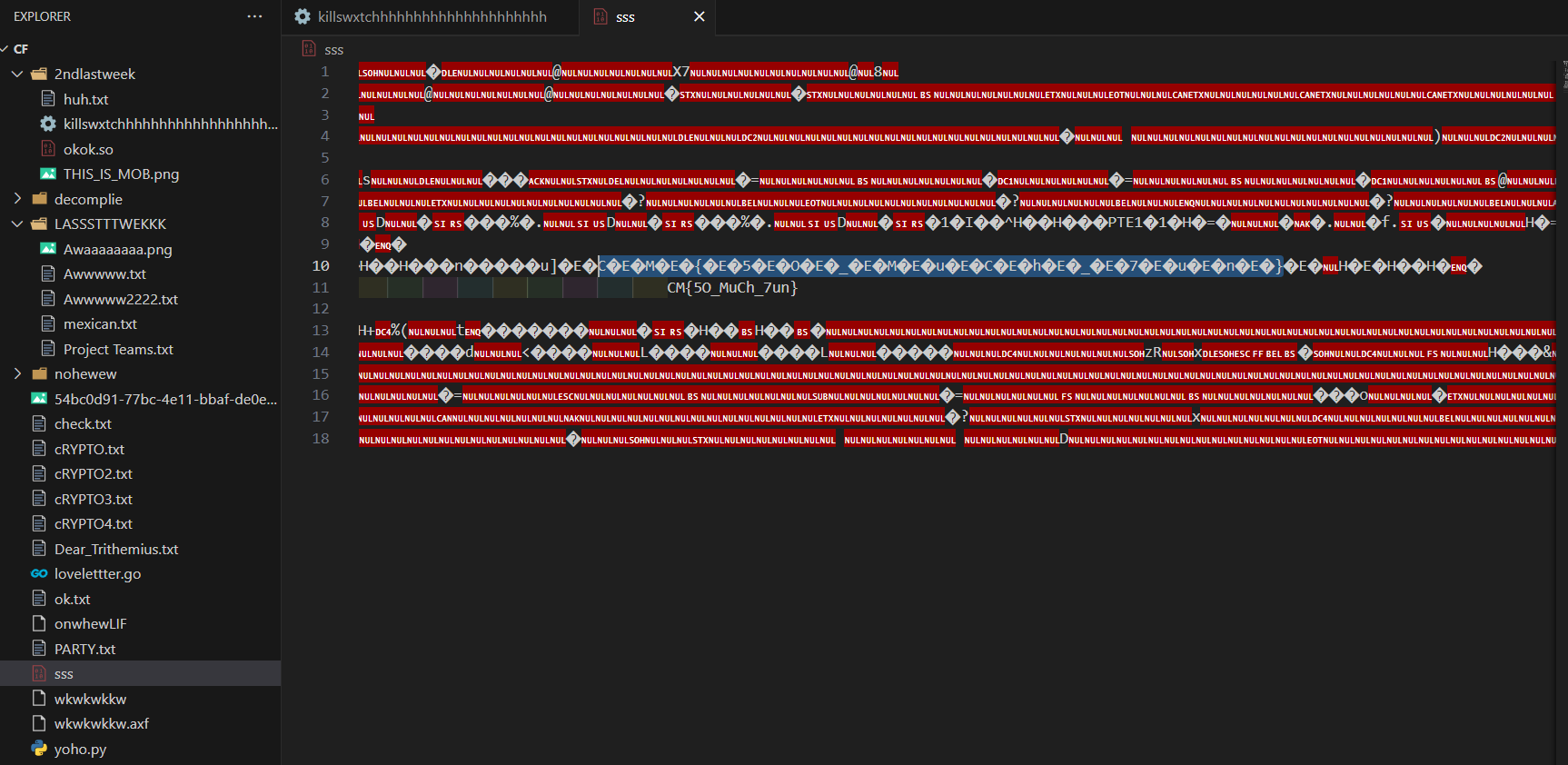
Solution
Provided a file with no extension. Adding “.txt”, we can see its contents. The flag is found when we remove the null values.
Flag
CM{5O_MuCh_7un}
Green Flags
Challenge Description
OLD CTF
Solution
The given flags in the picture represent the flag, the flags are from International maritime signal flags.
Flag
CM{NATO_SIGNALS}
Digital Black Hole
Challenge Description
OLD CTF
Solution
Provided a file with “.PNG”, converting it to “.txt” , we can see its contents. It consists of binary numbers, converting it to ASCII and to numbers we again get binary. Repeating the process we get a ciphered text. We convert it with Base62 to retrieve the flag
Flag
CM{N0t_64_Alway5}
Dear Trithemius,
Challenge Description
OLD CTF
Solution
Provided a LoveLetter and a Go code, there is a encrypted message in the love letter. By writing a python code to reverse the Go code we can retrieve the flag.
Flag
CM{LOVE_U_TRITHEMIUS}
I can't see it
Challenge Description
OLD CTF
Solution
We convert the given Braille text to retrieve the flag
Flag
CM{TH15_BR41LL3_1S_43AL}
My Secret X 'V' My Secret Y
Challenge Description
OLD CTF
Solution
Provided Cipher Text, we can convert it with XOR Cipher to retrieve the flag
Flag
CM{Th353_x0R_4r3_cR4zY}
We're rolling
Challenge Description
OLD CTF
Solution
Flag can be found in robots.txt https://ctf.cybermaterial.com/robots.txt
Flag
CM{RoOL_&_ROoL}
A Shakespearian Tragedy
Challenge Description
OLD CTF
Solution
Provided a URL and told there were hidden doors. Used DIRB to find active links and found.
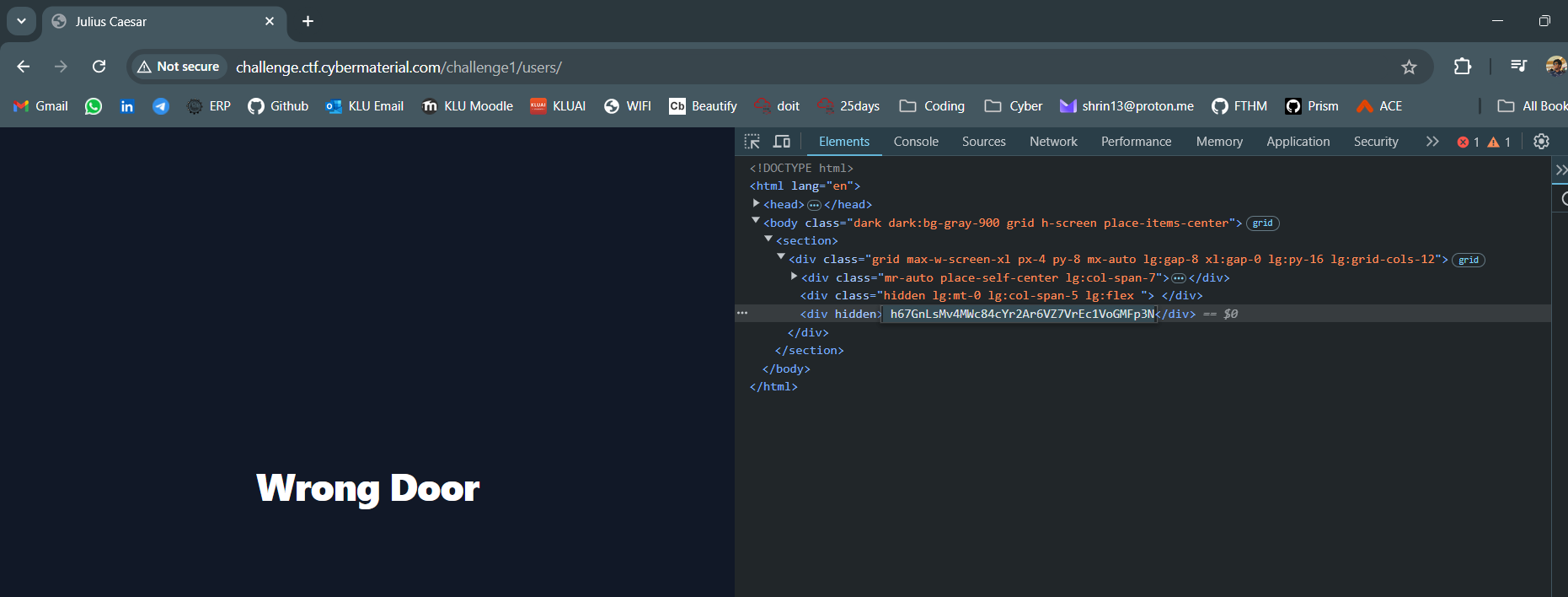
There was a hidden cipher text, we can convert it with Base58 to retrieve flag.
Flag
CM{i_c4me_i_s4w_i_c0nqu3r3d}
The Shell Shocker
Challenge Description
OLD CTF
Solution
Provided a URL and found the script.js in it. In it, it had a API url with POST requests for commands.
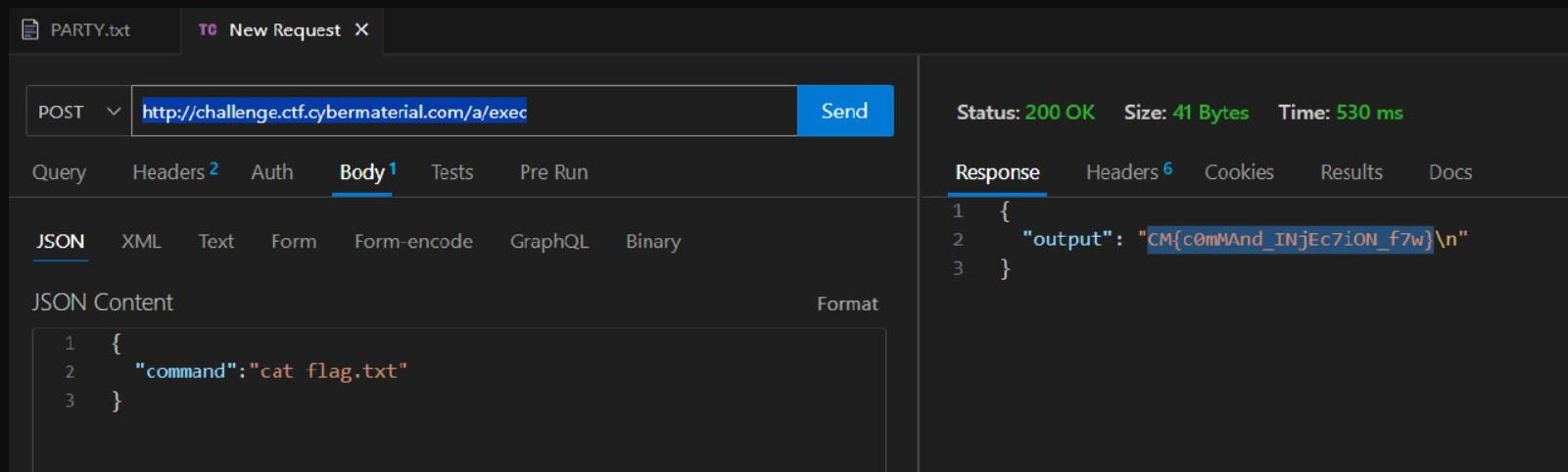
Flag
CM{c0mMAnd_INjEc7iON_f7w}
Drunken website
Challenge Description
OLD CTF
Solution
Provided with a URL, it had a button redirecting to the homepage. When we inspect the page we can find a hidden URL. When we Inspect the that page we can locate the flag
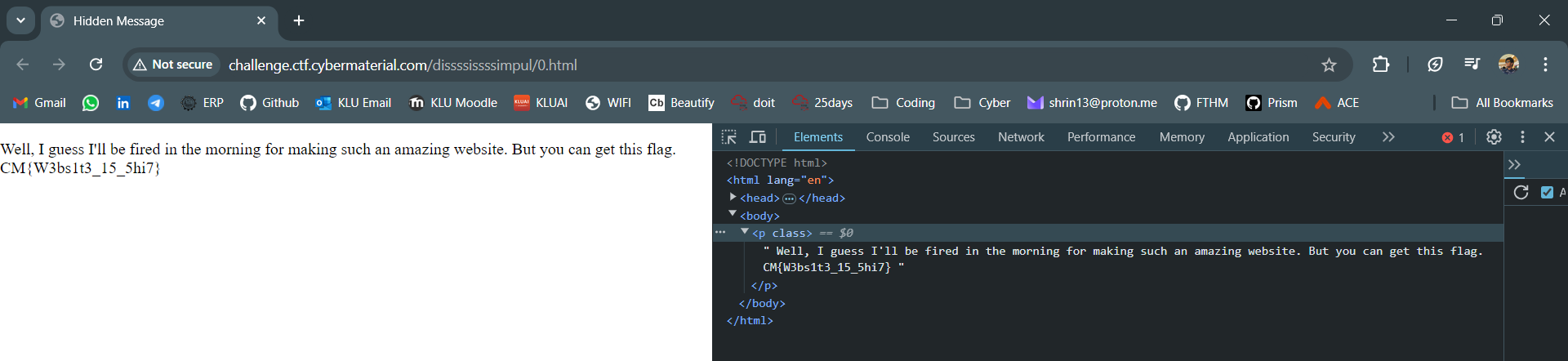
Flag
CM{W3bs1t3_15_5hi7}
Bidden Funhouse
Challenge Description
OLD CTF
Solution
Provided a URL, using the SSTImap tool I did Server-Side Template Injection. I was able to find the flag in app.py
Flag
CM{Y0u_4r3_a_r3A1Ly_go0D_nINj4}
CyberMaterial’s Cyber-Sleuth Newsletter
Challenge Description
OLD CTF
Solution
It mentions about a newsletter and it mentions about “A Hacker leaked unreleased Netflix content”. The flag can be found in a CyberMaterial Linkedin post.
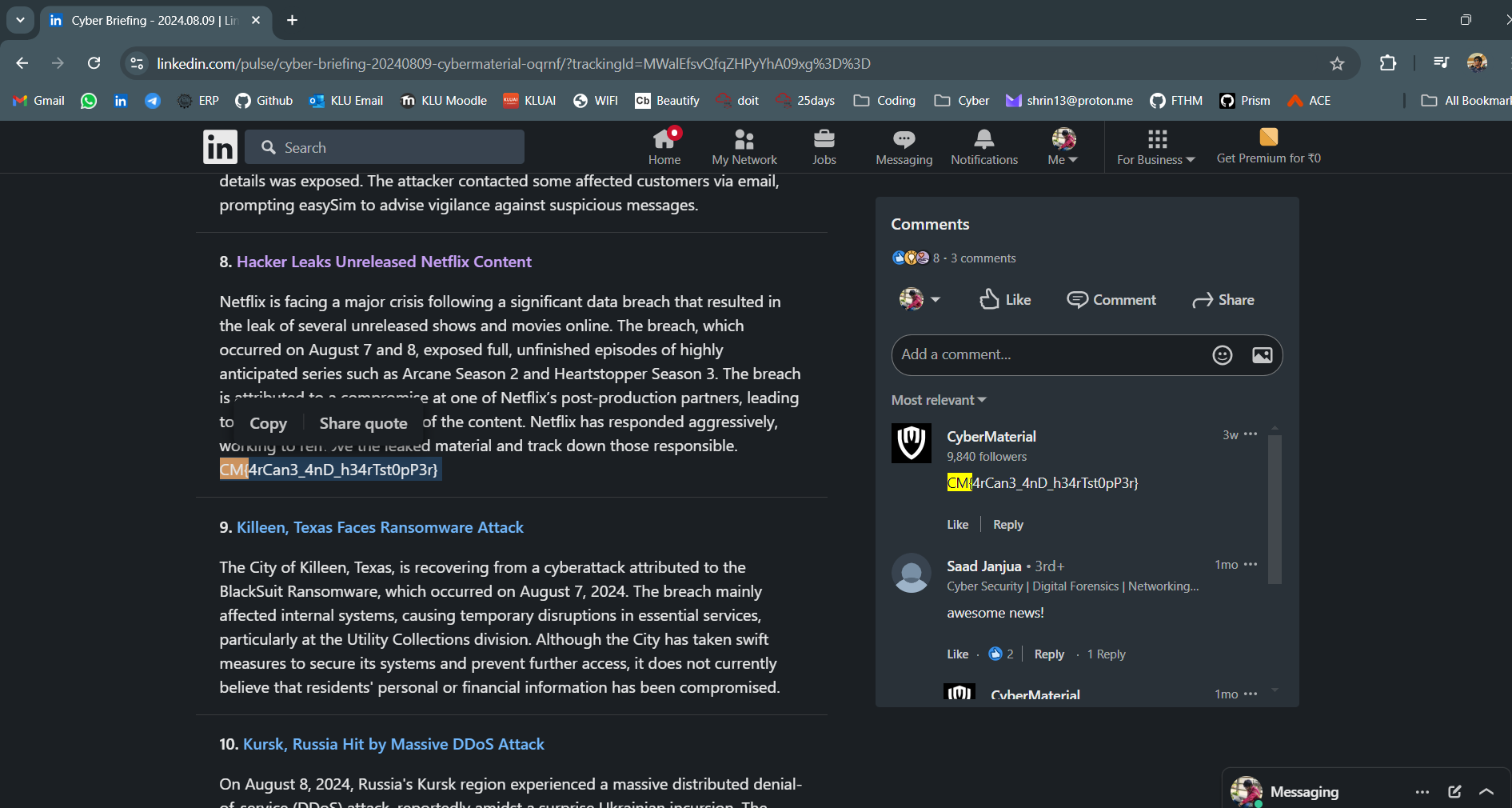
Flag
CM{4rCan3_4nD_h34rTst0pP3r}
APT Intel Hunt
Challenge Description
OLD CTF
Solution
It mentions about “Andariel” and “Lazarus”. There is an article about this topic.
https://cybermaterial.com/andariel-lazarus-group-threat-actor/ In between of all the hyperlinks there is a link to a pastebin https://pastebin.com/QUwg950y
In between of all the text there are random letters & numbers, grouping all of them we get a ciphertext. We can convert it from HEX to ASCII to normal.
Flag
CM{4pT_Gr0uP5_L4z4Ru5}
Meet me here !
Challenge Description
OLD CTF
Solution
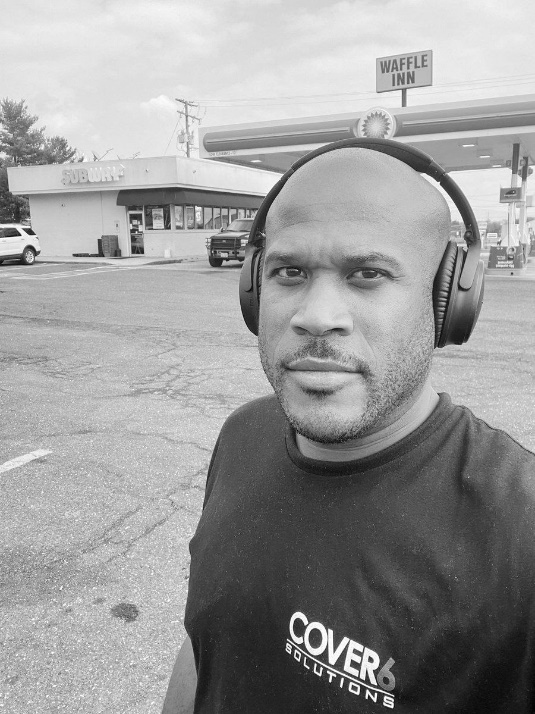
In the background we can see a subway and it looks like a petrol station. His TShirt says “Cover6 Solutions” so it must be near it. Cover6 Solutions is located in “Arlington, Virginia” as per their Linkedin so we if overlap them and cross verify with the subway we can find the road it is located in.

Flag
CM{Laurel_Hill_Rd}
Catch me !!!
Challenge Description
OLD CTF
Solution

By looking at this we can an Icon. By checking Google Maps Icons we can determine that it is a Museum. On the left we can slightly read the road name “Stewart ave”. By checking the museums on Stewart ave we can find the museums in the picture

Flag
CM{The_Mob_Museum}
Oops! Where Did I Hide the Flag?
Challenge Description
OLD CTF
Solution
The flag is in the description of video - https://youtu.be/iM4vtqkhmIo
Flag
CM{SuB5cR1b3_t0_0ur_Y0u7ub3_Ch4nN3L}